Create your own CA with TinyCA2 (part 2)
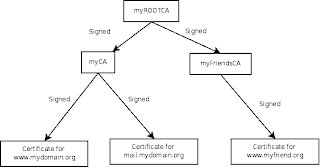
In part one of this series we created a root CA, a sub-CA and a certificate for our web site All certificates are stored in TinyCA2s configuration. In this part we will:
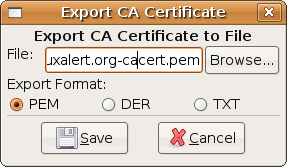 To be able to import the root CA certificate to Firefox we must export it from TinyCA2. In the main window of TinyCA2, open the CA-menu and select Open CA. Select your root CA. Select Export CA Certificate in the toolbar, which is the second icon from the right. You may change the file name. Press Save when ready.
To be able to import the root CA certificate to Firefox we must export it from TinyCA2. In the main window of TinyCA2, open the CA-menu and select Open CA. Select your root CA. Select Export CA Certificate in the toolbar, which is the second icon from the right. You may change the file name. Press Save when ready.
 Start Firefox, select the Edit-menu and Preferences. Click the Advanced icon and then the Encryption tab. Select View certificates and then the Authorities tab.
Start Firefox, select the Edit-menu and Preferences. Click the Advanced icon and then the Encryption tab. Select View certificates and then the Authorities tab. You can see all the CA:s you trust. Click Import and select the file with your exported root certificate. You can in the Downloading Certificate window control what purposes the certificate has. I select all three purposes.
You can see all the CA:s you trust. Click Import and select the file with your exported root certificate. You can in the Downloading Certificate window control what purposes the certificate has. I select all three purposes.

Click OK and leave the preferences. Then restart Firefox.
It is time to configure the web server. I assume that you already have an Apache http server running. First we must export the web sites certificate and encryption key. Since we signed the certificate with our sub-CA, we must also tell the web server to tell the web browser how to find the right root CA. This is done using a chain file that we export from TinyCA2 too.
 Return to TinyCA2 and verify that you have your sub-CA opened. Select the Certificates tab, right click on the web site's certificate and select Export certificate. You may change the file name, then click Save. I use the name of the web site dash cert dot pem as filename, i.e. www.linuxalert.org-cert.pem.
Return to TinyCA2 and verify that you have your sub-CA opened. Select the Certificates tab, right click on the web site's certificate and select Export certificate. You may change the file name, then click Save. I use the name of the web site dash cert dot pem as filename, i.e. www.linuxalert.org-cert.pem.
Do the same with the key. Select the Keys tab, right click on the web site's key and select Export key. You may change the file name. I use the name of the web site dash key dot pem as filename, i.e. www.linuxalert.org-key.pem. Do also select "without passphrase" - yes. This lets you start the web server without enter the certificates password. Then click Save. TinyCA2 will ask you for the password of the certificate for the web server.
Go to the CA tab to export the certificate chain. Select the right most icon in the tool bar and save the file.
Copy all three files to the web server's directory /etc/ssl/private/. Configure the web server to listen on the https port, number 443. In Ubuntu, this is done adding the line:
Listen 443
to the file /etc/apache2/ports.conf. Activate the ssl-module with the command:
sudo a2enmod ssl
Create a file in /etc/apache2/sites-enabled named after your site dash ssl, i.e. www.linuxalert.org-ssl:
<virtualhost 443="">
ServerAdmin A_correct_mailadr
ServerName www.linuxalert.org
DocumentRoot /var/www/
<directory>
Options +FollowSymLinks
AllowOverride All
order allow,deny
allow from all
RewriteBase /
</directory>
ScriptAlias /cgi-bin/ /usr/lib/cgi-bin/
<directory usr="" lib="" bin="">
AllowOverride None
Options ExecCGI -MultiViews +SymLinksIfOwnerMatch
Order allow,deny
Allow from all
</directory>
ErrorLog /var/log/apache2/www.linuxalert.org-ssl-error.log
# Possible values include: debug, info, notice, warn, error, crit,
# alert, emerg.
LogLevel warn
CustomLog /var/log/apache2/www.linuxalert.org-ssl-access.log combined
ServerSignature On
SSLEngine on
SSLCertificateFile /etc/ssl/private/www.linuxalert.org-cert.pem
SSLCertificateKeyFile /etc/ssl/private/www.linuxalert.org-key.pem
SSLCertificateChainFile /etc/ssl/private/Linuxalert.org-CA-cachain.pem
</virtualhost>
Set the parameters according to your site. Some part depends on how you have configured apache. The important part from this HowTo:s perspective is the SSL-parameters.
Restart apache:
sudo /etc/init.d/apache2 restart
Try to surf to your site. If everything works you will NOT get a dialog box were Firefox tells you that it does not recognize the sites certificate.
In the final part of this series we will integrate our root CA certificate with Ubuntus pre-installed certificates.
- export the root CA:s certificate
- import the root CA:s certificate into Firefox
- export the certificate for the web site
- configure our web server to use the web site certificate
 To be able to import the root CA certificate to Firefox we must export it from TinyCA2. In the main window of TinyCA2, open the CA-menu and select Open CA. Select your root CA. Select Export CA Certificate in the toolbar, which is the second icon from the right. You may change the file name. Press Save when ready.
To be able to import the root CA certificate to Firefox we must export it from TinyCA2. In the main window of TinyCA2, open the CA-menu and select Open CA. Select your root CA. Select Export CA Certificate in the toolbar, which is the second icon from the right. You may change the file name. Press Save when ready. Start Firefox, select the Edit-menu and Preferences. Click the Advanced icon and then the Encryption tab. Select View certificates and then the Authorities tab.
Start Firefox, select the Edit-menu and Preferences. Click the Advanced icon and then the Encryption tab. Select View certificates and then the Authorities tab. You can see all the CA:s you trust. Click Import and select the file with your exported root certificate. You can in the Downloading Certificate window control what purposes the certificate has. I select all three purposes.
You can see all the CA:s you trust. Click Import and select the file with your exported root certificate. You can in the Downloading Certificate window control what purposes the certificate has. I select all three purposes.
Click OK and leave the preferences. Then restart Firefox.
It is time to configure the web server. I assume that you already have an Apache http server running. First we must export the web sites certificate and encryption key. Since we signed the certificate with our sub-CA, we must also tell the web server to tell the web browser how to find the right root CA. This is done using a chain file that we export from TinyCA2 too.
 Return to TinyCA2 and verify that you have your sub-CA opened. Select the Certificates tab, right click on the web site's certificate and select Export certificate. You may change the file name, then click Save. I use the name of the web site dash cert dot pem as filename, i.e. www.linuxalert.org-cert.pem.
Return to TinyCA2 and verify that you have your sub-CA opened. Select the Certificates tab, right click on the web site's certificate and select Export certificate. You may change the file name, then click Save. I use the name of the web site dash cert dot pem as filename, i.e. www.linuxalert.org-cert.pem.Do the same with the key. Select the Keys tab, right click on the web site's key and select Export key. You may change the file name. I use the name of the web site dash key dot pem as filename, i.e. www.linuxalert.org-key.pem. Do also select "without passphrase" - yes. This lets you start the web server without enter the certificates password. Then click Save. TinyCA2 will ask you for the password of the certificate for the web server.
Go to the CA tab to export the certificate chain. Select the right most icon in the tool bar and save the file.
Copy all three files to the web server's directory /etc/ssl/private/. Configure the web server to listen on the https port, number 443. In Ubuntu, this is done adding the line:
Listen 443
to the file /etc/apache2/ports.conf. Activate the ssl-module with the command:
sudo a2enmod ssl
Create a file in /etc/apache2/sites-enabled named after your site dash ssl, i.e. www.linuxalert.org-ssl:
<virtualhost 443="">
ServerAdmin A_correct_mailadr
ServerName www.linuxalert.org
DocumentRoot /var/www/
<directory>
Options +FollowSymLinks
AllowOverride All
order allow,deny
allow from all
RewriteBase /
</directory>
ScriptAlias /cgi-bin/ /usr/lib/cgi-bin/
<directory usr="" lib="" bin="">
AllowOverride None
Options ExecCGI -MultiViews +SymLinksIfOwnerMatch
Order allow,deny
Allow from all
</directory>
ErrorLog /var/log/apache2/www.linuxalert.org-ssl-error.log
# Possible values include: debug, info, notice, warn, error, crit,
# alert, emerg.
LogLevel warn
CustomLog /var/log/apache2/www.linuxalert.org-ssl-access.log combined
ServerSignature On
SSLEngine on
SSLCertificateFile /etc/ssl/private/www.linuxalert.org-cert.pem
SSLCertificateKeyFile /etc/ssl/private/www.linuxalert.org-key.pem
SSLCertificateChainFile /etc/ssl/private/Linuxalert.org-CA-cachain.pem
</virtualhost>
Set the parameters according to your site. Some part depends on how you have configured apache. The important part from this HowTo:s perspective is the SSL-parameters.
Restart apache:
sudo /etc/init.d/apache2 restart
Try to surf to your site. If everything works you will NOT get a dialog box were Firefox tells you that it does not recognize the sites certificate.
In the final part of this series we will integrate our root CA certificate with Ubuntus pre-installed certificates.
Comments